WebSocket
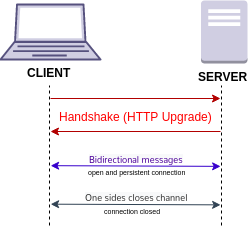 A diagram describing a connection using WebSocket | |
| International standard | RFC 6455 |
|---|---|
| Developed by | IETF |
| Industry | Computer science |
| Connector type | TCP |
| Website | https://websockets.spec.whatwg.org/ |
WebSocket is a computer communications protocol, providing a simultaneous two-way communication channel over a single Transmission Control Protocol (TCP) connection. The WebSocket protocol was standardized by the IETF as RFC 6455 in 2011. The current specification allowing web applications to use this protocol is known as WebSockets.[1] It is a living standard maintained by the WHATWG and a successor to The WebSocket API from the W3C.[2]
WebSocket is distinct from HTTP used to serve most webpages. Although they are different, RFC 6455 states that WebSocket "is designed to work over HTTP ports 443 and 80 as well as to support HTTP proxies and intermediaries", thus making it compatible with HTTP. To achieve compatibility, the WebSocket handshake uses the HTTP Upgrade header[3] to change from the HTTP protocol to the WebSocket protocol.
The WebSocket protocol enables full-duplex interaction between a web browser (or other client application) and a web server with lower overhead than half-duplex alternatives such as HTTP polling, facilitating real-time data transfer from and to the server. This is made possible by providing a standardized way for the server to send content to the client without being first requested by the client, and allowing messages to be passed back and forth while keeping the connection open. In this way, a two-way ongoing conversation can take place between the client and the server. The communications are usually done over TCP port number 443 (or 80 in the case of unsecured connections), which is beneficial for environments that block non-web Internet connections using a firewall. Additionally, WebSocket enables streams of messages on top of TCP. TCP alone deals with streams of bytes with no inherent concept of a message. Similar two-way browser–server communications have been achieved in non-standardized ways using stopgap technologies such as Comet or Adobe Flash Player.[4]
Most browsers support the protocol, including Google Chrome, Firefox, Microsoft Edge, Internet Explorer, Safari and Opera.[5]
The WebSocket protocol specification defines ws (WebSocket) and wss (WebSocket Secure) as two new uniform resource identifier (URI) schemes[6] that are used for unencrypted and encrypted connections respectively. Apart from the scheme name and fragment (i.e. # is not supported), the rest of the URI components are defined to use URI generic syntax.[7]
History
[edit]WebSocket was first referenced as TCPConnection in the HTML5 specification, as a placeholder for a TCP-based socket API.[8] In June 2008, a series of discussions were led by Michael Carter that resulted in the first version of the protocol known as WebSocket.[9] Before WebSocket, port 80 full-duplex communication was attainable using Comet channels; however, Comet implementation is nontrivial, and due to the TCP handshake and HTTP header overhead, it is inefficient for small messages. The WebSocket protocol aims to solve these problems without compromising the security assumptions of the web. The name "WebSocket" was coined by Ian Hickson and Michael Carter shortly thereafter through collaboration on the #whatwg IRC chat room,[10] and subsequently authored for inclusion in the HTML5 specification by Ian Hickson. In December 2009, Google Chrome 4 was the first browser to ship full support for the standard, with WebSocket enabled by default.[11] Development of the WebSocket protocol was subsequently moved from the W3C and WHATWG group to the IETF in February 2010, and authored for two revisions under Ian Hickson.[12]
After the protocol was shipped and enabled by default in multiple browsers, the RFC 6455 was finalized under Ian Fette in December 2011.
RFC 7692 introduced compression extension to WebSocket using the DEFLATE algorithm on a per-message basis.
Client example
[edit]<!DOCTYPE html>
<script>
// Connect to server
ws = new WebSocket("ws://127.0.0.1/scoreboard") // Local server
// ws = new WebSocket("wss://game.example.com/scoreboard") // Remote server
ws.onopen = () => {
console.log("Connection opened")
ws.send("Hi server, please send me the score of yesterday's game")
}
ws.onmessage = (event) => {
console.log("Data received", event.data)
ws.close() // We got the score so we don't need the connection anymore
}
ws.onclose = (event) => {
console.log("Connection closed", event.code, event.reason, event.wasClean)
}
ws.onerror = () => {
console.log("Connection closed due to error")
}
</script>
Server example
[edit]from socket import socket
from base64 import b64encode
from hashlib import sha1
MAGIC = b"258EAFA5-E914-47DA-95CA-C5AB0DC85B11"
# Create socket and listen at port 80
ws = socket()
ws.bind(("", 80))
ws.listen()
conn, addr = ws.accept()
# Parse request
for line in conn.recv(4096).split(b"\r\n"):
if line.startswith(b"Sec-WebSocket-Key"):
nonce = line.split(b":")[1].strip()
# Format response
response = f"""\
HTTP/1.1 101 Switching Protocols
Upgrade: websocket
Connection: Upgrade
Sec-WebSocket-Accept: {b64encode(sha1(nonce + MAGIC).digest()).decode()}
"""
conn.send(response.replace("\n", "\r\n").encode())
while True: # decode messages from the client
header = conn.recv(2)
FIN = bool(header[0] & 0x80) # bit 0
assert FIN == 1, "We only support unfragmented messages"
opcode = header[0] & 0xf # bits 4-7
assert opcode == 1 or opcode == 2, "We only support data messages"
masked = bool(header[1] & 0x80) # bit 8
assert masked, "The client must mask all frames"
payload_size = header[1] & 0x7f # bits 9-15
assert payload_size <= 125, "We only support small messages"
masking_key = conn.recv(4)
payload = bytearray(conn.recv(payload_size))
for i in range(payload_size):
payload[i] = payload[i] ^ masking_key[i % 4]
print(payload)
Web API
[edit]A web application (e.g. web browser) may use the WebSocket interface to connect to a WebSocket server.
| Type | Name[13] | Description |
|---|---|---|
| Constructor | ws = new WebSocket(url [, protocols ])
|
Start opening handshake with a WebSocket server.[14]
|
| Method | ws.send(data)
|
Send data. data must be string, Blob, ArrayBuffer or ArrayBufferView. Throw InvalidStateError if ws.readyState is WebSocket.CONNECTING.
|
ws.close([ code ] [, reason ])
|
Start closing handshake.[15]
| |
| Event | ws.onopen = (event) => {}
|
Opening handshake succeeded. event type is Event.
|
ws.onmessage = (event) => {}
|
Data received. event type is MessageEvent. event.data contains the data received, of type:[16]
| |
ws.onclose = (event) => {}
|
The underlying TCP connection closed. event type is CloseEvent containing:[17][18][19][20]
Note:
| |
ws.onerror = (event) => {}
|
Connection closed due to error. event type is Event.
| |
| Attribute | ws.binaryType
|
A string indicating the type of event.data in ws.onmessage when binary data is received. Initially set to "blob" (Blob object). May be changed to "arraybuffer" (ArrayBuffer object).
|
| Read-only attribute | ws.url
|
The URL given to the WebSocket constructor. |
ws.bufferedAmount
|
The number of bytes waiting to be transmitted. | |
ws.protocol
|
The protocol accepted by the server, or an empty string if the client did not specify protocols in the WebSocket constructor.
| |
ws.extensions
|
The extensions accepted by the server. | |
ws.readyState
|
The connection state. It is one of the constants below. | |
| Constant | WebSocket.CONNECTING = 0
|
Waiting opening handshake.[21][22] |
WebSocket.OPEN = 1
|
Opening handshake succeeded. The client and server may message each other.[23][24] | |
WebSocket.CLOSING = 2
|
Waiting closing handshake. Either ws.close() was called or the server sent a Close frame.[25][26]
| |
WebSocket.CLOSED = 3
|
The underlying TCP connection is closed.[27][17][18] |
Protocol
[edit]Steps:
- Opening handshake (HTTP request + HTTP response) to establish a connection.
- Data messages to transfer application data.
- Closing handshake (two Close frames) to close the connection.
Opening handshake
[edit]The client sends an HTTP request (method GET, version ≥ 1.1) and the server returns an HTTP response with status code 101 (Switching Protocols) on success. This means a WebSocket server can use the same port as HTTP (80) and HTTPS (443) because the handshake is compatible with HTTP.[28]
Side
|
Header | Value | Mandatory |
|---|---|---|---|
Request
|
Origin | Varies | Yes (for browser clients)[29] |
| Host | Varies | Yes | |
| Sec-WebSocket-Version | 13[30] | ||
| Sec-WebSocket-Key | base64-encode(16-byte random nonce)[31] | ||
Response
|
Sec-WebSocket-Accept | base64-encode(sha1(Sec-WebSocket-Key + "258EAFA5-E914-47DA-95CA-C5AB0DC85B11"))[32] | |
Both
|
Connection | Upgrade[33][34] | |
| Upgrade | websocket[35][36] | ||
| Sec-WebSocket-Protocol | The request may contain a comma-separated list of strings (ordered by preference) indicating application-level protocols (built on top of WebSocket data messages) the client wishes to use.[37] If the client sends this header, the server response must be one of the values from the list. | Optional | |
| Sec-WebSocket-Extensions | |||
| Other headers | Varies |
Example request:[38]
GET /chat HTTP/1.1
Host: server.example.com
Upgrade: websocket
Connection: Upgrade
Sec-WebSocket-Key: x3JJHMbDL1EzLkh9GBhXDw==
Sec-WebSocket-Protocol: chat, superchat
Sec-WebSocket-Version: 13
Origin: http://example.com
Example response:
HTTP/1.1 101 Switching Protocols
Upgrade: websocket
Connection: Upgrade
Sec-WebSocket-Accept: HSmrc0sMlYUkAGmm5OPpG2HaGWk=
Sec-WebSocket-Protocol: chat
In HTTP each line ends in \r\n and the last line is empty.
# Calculate Sec-WebSocket-Accept using Sec-WebSocket-Key
from base64 import b64encode
from hashlib import sha1
from os import urandom
# key = b64encode(urandom(16)) # Client should do this
key = b"x3JJHMbDL1EzLkh9GBhXDw==" # Value in example request above
magic = b"258EAFA5-E914-47DA-95CA-C5AB0DC85B11" # Protocol constant
print(b64encode(sha1(key + magic).digest()))
# Output: HSmrc0sMlYUkAGmm5OPpG2HaGWk=
Once the connection is established, communication switches to a binary frame-based protocol which does not conform to the HTTP protocol.
Sec-WebSocket-Key and Sec-WebSocket-Accept are intended to prevent a caching proxy from re-sending a previous WebSocket conversation,[39] and does not provide any authentication, privacy, or integrity.
Though some servers accept a short Sec-WebSocket-Key, many modern servers will reject the request with error "invalid Sec-WebSocket-Key header".
Frame-based message
[edit]After the opening handshake, the client and server can, at any time, send messages to each other, such as data messages (text or binary) and control messages (close, ping, pong). A message is composed of one or more frames.
Fragmentation allows a message to be split into two or more frames. It enables sending messages with initial data available but complete length unknown. Without fragmentation, the whole message must be sent in one frame, so the complete length is needed before the first byte can be sent, which requires a buffer.[40] It also enables multiplexing several streams simultaneously (e.g. to avoid monopolizing a socket for a single large payload).[41]
- An unfragmented message consists of a single frame with
FIN = 1andopcode ≠ 0. - A fragmented message consists of a single frame with
FIN = 0andopcode ≠ 0, followed by zero or more frames withFIN = 0andopcode = 0, and terminated by a single frame withFIN = 1andopcode = 0.
Frame structure
[edit]| Index (in bits) |
Field | Size (in bits) |
Description | |
|---|---|---|---|---|
| 0 | FIN[42] | 1 |
| |
| 1 | RSV1 | 1 | Must be 0 unless defined by an extension.[43] | |
| 2 | RSV2 | 1 | ||
| 3 | RSV3 | 1 | ||
| 4 | Opcode | 4 | See opcodes below. | |
| 8 | Masked[44] | 1 |
| |
| 9 | Payload length[45] | 7, 7+16 or 7+64 | Length of the payload (extension data + application data) in bytes.
| |
| Varies | Masking key | 0 or 32 | A client must mask all frames sent to the server. A server must not mask any frames sent to the client.[46]
Frame masking applies XOR between the masking key (a four-byte random nonce) and the payload data. The following algorithm is used to mask/unmask a frame:[47]for i = 0 to payload_length - 1
payload[i] = payload[i] xor masking_key[i modulo 4]
| |
| Payload | Extension data | Payload length (in bytes) | Must be empty unless defined by an extension. | |
| Application data | Depends on the opcode. | |||
Opcodes
[edit]| Frame type | Opcode | Related | Description | Purpose | Fragmentable
|
Max. payload length | |
|---|---|---|---|---|---|---|---|
| Continuation | 0 | Identifies an intermediate frame of a fragmented message. | bytes | ||||
| Data frame | Text | 1 | send(), onmessage
|
UTF-8 encoded application text. | Application data | Yes | |
| Binary | 2 | Application binary data. | |||||
| 3–7 | Reserved | ||||||
| Control frame | Close | 8 | close(), onclose
|
A Close frame is sent to start the closing handshake which may prevent data loss by complementing the TCP closing handshake.[48] No frame can be sent after a Close frame. If a Close frame is received and no prior Close frame was sent, a response Close frame with the same payload must be sent. The payload is optional, but if present, it must start with a two-byte big-endian unsigned integer reason code, optionally followed by a UTF-8 encoded reason message not longer than 123 bytes.[49] | Protocol state | No | 125 bytes |
| Ping | 9 | May be used for latency measurement, keepalive and heartbeat. Both sides can initiate a ping (with any payload). Whoever receives it must immediately send back a pong with the same payload. A pong should be ignored if no prior ping was sent.[50][51] | |||||
| Pong | 10 | ||||||
| 11–15 | Reserved | ||||||
Status codes
[edit]| Range[52] | Allowed in Close frame | Code | Description |
|---|---|---|---|
| 0–999 | No | Unused | |
| 1000–2999 (Protocol) | Yes | 1000 | Normal closure. |
| 1001 | Going away (e.g. browser tab closed). | ||
| 1002 | Protocol error. | ||
| 1003 | Unsupported data (e.g. endpoint only understands text but received binary). | ||
| No | 1004 | Reserved for future usage | |
| 1005 | No code received. | ||
| 1006 | Connection closed abnormally (closing handshake did not occur). | ||
| Yes | 1007 | Invalid payload data (e.g. non UTF-8 data in a text message). | |
| 1008 | Policy violated. | ||
| 1009 | Message too big. | ||
| 1010 | Unsupported extension. The client should write the extensions it expected the server to support in the payload. | ||
| 1011 | Internal server error. | ||
| No | 1015 | TLS handshake failure. | |
| 3000–3999 | Yes | Used by libraries, frameworks and applications. | |
| 4000–4999 | Private use. |
Browser support
[edit]A secure version of the WebSocket protocol is implemented in Firefox 6,[54] Safari 6, Google Chrome 14,[55] Opera 12.10 and Internet Explorer 10.[56] A detailed protocol test suite report[57] lists the conformance of those browsers to specific protocol aspects.
An older, less secure version of the protocol was implemented in Opera 11 and Safari 5, as well as the mobile version of Safari in iOS 4.2.[58] The BlackBerry Browser in OS7 implements WebSockets.[59] Because of vulnerabilities, it was disabled in Firefox 4 and 5,[60] and Opera 11.[61] Using browser developer tools, developers can inspect the WebSocket handshake as well as the WebSocket frames.[62]
Protocol Version
|
Draft date | Internet Explorer | Firefox[63] (PC) |
Firefox (Android) |
Chrome (PC, Mobile) |
Safari (Mac, iOS) |
Opera (PC, Mobile) |
Android Browser |
|---|---|---|---|---|---|---|---|---|
| hixie-75 | February 4, 2010 | 4 | 5.0.0 | |||||
| hixie-76 hybi-00 |
May 6, 2010 May 23, 2010 |
4.0 (disabled) |
6 | 5.0.1 | 11.00 (disabled) |
|||
| hybi-07, v7 | April 22, 2011 | 6[64][a] | ||||||
| hybi-10, v8 | July 11, 2011 | 7[66][a] | 7 | 14[67] | ||||
| RFC 6455, v13 | December, 2011 | 10[68] | 11 | 11 | 16[69] | 6 | 12.10[70] | 4.4 |
Server implementations
[edit]- Nginx has supported WebSockets since 2013, implemented in version 1.3.13[71] including acting as a reverse proxy and load balancer of WebSocket applications.[72]
- Apache HTTP Server has supported WebSockets since July, 2013, implemented in version 2.4.5[73][74]
- Internet Information Services added support for WebSockets in version 8 which was released with Windows Server 2012.[75]
- lighttpd has supported WebSockets since 2017, implemented in lighttpd 1.4.46.[76] lighttpd mod_proxy can act as a reverse proxy and load balancer of WebSocket applications. lighttpd mod_wstunnel can act as a WebSocket endpoint to transmit arbitrary data, including in JSON format, to a backend application. lighttpd supports WebSockets over HTTP/2 since 2022, implemented in lighttpd 1.4.65.[77]
Security considerations
[edit]Unlike regular cross-domain HTTP requests, WebSocket requests are not restricted by the same-origin policy. Therefore, WebSocket servers must validate the "Origin" header against the expected origins during connection establishment, to avoid cross-site WebSocket hijacking attacks (similar to cross-site request forgery), which might be possible when the connection is authenticated with cookies or HTTP authentication. It is better to use tokens or similar protection mechanisms to authenticate the WebSocket connection when sensitive (private) data is being transferred over the WebSocket.[78] A live example of vulnerability was seen in 2020 in the form of Cable Haunt.
Proxy traversal
[edit]WebSocket protocol client implementations try to detect whether the user agent is configured to use a proxy when connecting to destination host and port, and if it is, uses HTTP CONNECT method to set up a persistent tunnel.
While the WebSocket protocol itself is unaware of proxy servers and firewalls, it features an HTTP-compatible handshake, thus allowing HTTP servers to share their default HTTP and HTTPS ports (80 and 443 respectively) with a WebSocket gateway or server. The WebSocket protocol defines a ws:// and wss:// prefix to indicate a WebSocket and a WebSocket Secure connection respectively. Both schemes use an HTTP upgrade mechanism to upgrade to the WebSocket protocol. Some proxy servers are transparent and work fine with WebSocket; others will prevent WebSocket from working correctly, causing the connection to fail. In some cases, additional proxy-server configuration may be required, and certain proxy servers may need to be upgraded to support WebSocket.
If unencrypted WebSocket traffic flows through an explicit or a transparent proxy server without WebSockets support, the connection will likely fail.[79]
If an encrypted WebSocket connection is used, then the use of Transport Layer Security (TLS) in the WebSocket Secure connection ensures that an HTTP CONNECT command is issued when the browser is configured to use an explicit proxy server. This sets up a tunnel, which provides low-level end-to-end TCP communication through the HTTP proxy, between the WebSocket Secure client and the WebSocket server. In the case of transparent proxy servers, the browser is unaware of the proxy server, so no HTTP CONNECT is sent. However, since the wire traffic is encrypted, intermediate transparent proxy servers may simply allow the encrypted traffic through, so there is a much better chance that the WebSocket connection will succeed if WebSocket Secure is used. Using encryption is not free of resource cost, but often provides the highest success rate, since it would be travelling through a secure tunnel.
A mid-2010 draft (version hixie-76) broke compatibility with reverse proxies and gateways by including eight bytes of key data after the headers, but not advertising that data in a Content-Length: 8 header.[80] This data was not forwarded by all intermediates, which could lead to protocol failure. More recent drafts (e.g., hybi-09[81]) put the key data in a Sec-WebSocket-Key header, solving this problem.
See also
[edit]Notes
[edit]References
[edit]- ^ "WebSockets Standard". websockets.spec.whatwg.org. Archived from the original on 2023-03-12. Retrieved 2022-05-16.
- ^ "The WebSocket API". www.w3.org. Archived from the original on 2022-06-08. Retrieved 2022-05-16.
- ^ Ian Fette; Alexey Melnikov (December 2011). "Relationship to TCP and HTTP". RFC 6455 The WebSocket Protocol. IETF. sec. 1.7. doi:10.17487/RFC6455. RFC 6455.
- ^ "Adobe Flash Platform – Sockets". help.adobe.com. Archived from the original on 2021-04-18. Retrieved 2021-07-28.
TCP connections require a "client" and a "server". Flash Player can create client sockets.
- ^ "The WebSocket API (WebSockets)". MDN Web Docs. Mozilla Developer Network. 2023-04-06. Archived from the original on 2021-07-28. Retrieved 2021-07-26.
- ^ Graham Klyne, ed. (2011-11-14). "IANA Uniform Resource Identifier (URI) Schemes". Internet Assigned Numbers Authority. Archived from the original on 2013-04-25. Retrieved 2011-12-10.
- ^ Ian Fette; Alexey Melnikov (December 2011). "WebSocket URIs". RFC 6455 The WebSocket Protocol. IETF. sec. 3. doi:10.17487/RFC6455. RFC 6455.
- ^ "HTML 5". www.w3.org. Archived from the original on 2016-09-16. Retrieved 2016-04-17.
- ^ "[whatwg] TCPConnection feedback from Michael Carter on 2008-06-18 (whatwg.org from June 2008)". lists.w3.org. Archived from the original on 2016-04-27. Retrieved 2016-04-17.
- ^ "IRC logs: freenode / #whatwg / 20080618". krijnhoetmer.nl. Archived from the original on 2016-08-21. Retrieved 2016-04-18.
- ^ "Web Sockets Now Available In Google Chrome". Chromium Blog. Archived from the original on 2021-12-09. Retrieved 2016-04-17.
- ^ <ian@hixie.ch>, Ian Hickson (6 May 2010). "The WebSocket protocol". Ietf Datatracker. Archived from the original on 2017-03-17. Retrieved 2016-04-17.
- ^ "Interface definition". WHATWG. Archived from the original on 2023-03-12. Retrieved 2024-04-10.
- ^ "new WebSocket(url, protocols)". WHATWG. Archived from the original on 2023-03-12. Retrieved 2024-04-30.
- ^ "close(code, reason)". WHATWG. Archived from the original on 2023-03-12. Retrieved 2024-04-10.
- ^ "When a WebSocket message has been received". WHATWG. Archived from the original on 2023-03-12. Retrieved 2024-04-13.
- ^ a b "When the WebSocket connection is closed; substep 3". WHATWG. Archived from the original on 2023-03-12. Retrieved 2024-04-13.
- ^ a b The WebSocket Connection is Closed. sec. 7.1.4. doi:10.17487/RFC6455. RFC 6455.
- ^ The WebSocket Connection Close Code. sec. 7.1.5. doi:10.17487/RFC6455. RFC 6455.
- ^ The WebSocket Connection Close Reason. sec. 7.1.6. doi:10.17487/RFC6455. RFC 6455.
- ^ "CONNECTING". WHATWG. Archived from the original on 2023-03-12. Retrieved 2024-04-13.
- ^ Client Requirements. p. 14. sec. 4.1. doi:10.17487/RFC6455. RFC 6455.
- ^ "OPEN". WHATWG. Archived from the original on 2023-03-12. Retrieved 2024-04-10.
- ^ _The WebSocket Connection is Established_. p. 20. doi:10.17487/RFC6455. RFC 6455.
- ^ "CLOSING". WHATWG. Archived from the original on 2023-03-12. Retrieved 2024-04-10.
- ^ The WebSocket Closing Handshake is Started. sec. 7.1.3. doi:10.17487/RFC6455. RFC 6455.
- ^ "CLOSED". WHATWG. Archived from the original on 2023-03-12. Retrieved 2024-04-10.
- ^ Opening Handshake. sec. 1.3. doi:10.17487/RFC6455. RFC 6455.
- ^ Client requirement 8. p. 18. doi:10.17487/RFC6455. RFC 6455.
- ^ Client requirement 9. p. 18. doi:10.17487/RFC6455. RFC 6455.
- ^ Client requirement 7. p. 18. doi:10.17487/RFC6455. RFC 6455.
- ^ Server step 5.4. p. 24. doi:10.17487/RFC6455. RFC 6455.
- ^ Client requirement 6. p. 18. doi:10.17487/RFC6455. RFC 6455.
- ^ Server step 5.3. p. 24. doi:10.17487/RFC6455. RFC 6455.
- ^ Client requirement 5. p. 17. doi:10.17487/RFC6455. RFC 6455.
- ^ Server step 5.2. p. 24. doi:10.17487/RFC6455. RFC 6455.
- ^ Client requirement 10. p. 18. doi:10.17487/RFC6455. RFC 6455.
- ^ Protocol Overview. sec. 1.2. doi:10.17487/RFC6455. RFC 6455.
- ^ "Main Goal of WebSocket protocol". IETF. Archived from the original on 22 April 2016. Retrieved 25 July 2015.
The computation [...] is meant to prevent a caching intermediary from providing a WS-client with a cached WS-server reply without actual interaction with the WS-server.
- ^ Fragmentation. sec. 5.4. doi:10.17487/RFC6455. RFC 6455.
- ^ John A. Tamplin; Takeshi Yoshino (2013). A Multiplexing Extension for WebSockets. IETF. I-D draft-ietf-hybi-websocket-multiplexing.
- ^ FIN. p. 28. doi:10.17487/RFC6455. RFC 6455.
- ^ RSV1, RSV2, RSV3. p. 28. doi:10.17487/RFC6455. RFC 6455.
- ^ Mask. p. 29. doi:10.17487/RFC6455. RFC 6455.
- ^ Payload length. p. 29. doi:10.17487/RFC6455. RFC 6455.
- ^ Overview. sec. 5.1. doi:10.17487/RFC6455. RFC 6455.
- ^ Client-to-Server Masking. sec. 5.3. doi:10.17487/RFC6455. RFC 6455.
- ^ Closing Handshake. sec. 1.4. doi:10.17487/RFC6455. RFC 6455.
- ^ Close. sec. 5.5.1. doi:10.17487/RFC6455. RFC 6455.
- ^ Ping. sec. 5.5.2. doi:10.17487/RFC6455. RFC 6455.
- ^ Pong. sec. 5.5.3. doi:10.17487/RFC6455. RFC 6455.
- ^ Reserved Status Code Ranges. sec. 7.4.2. doi:10.17487/RFC6455. RFC 6455.
- ^ Defined Status Codes. sec. 7.4.1. doi:10.17487/RFC6455. RFC 6455.
- ^ Dirkjan Ochtman (May 27, 2011). "WebSocket enabled in Firefox 6". Mozilla.org. Archived from the original on 2012-05-26. Retrieved 2011-06-30.
- ^ "Chromium Web Platform Status". Archived from the original on 2017-03-04. Retrieved 2011-08-03.
- ^ "WebSockets (Windows)". Microsoft. 2012-09-28. Archived from the original on 2015-03-25. Retrieved 2012-11-07.
- ^ "WebSockets Protocol Test Report". Tavendo.de. 2011-10-27. Archived from the original on 2016-09-22. Retrieved 2011-12-10.
- ^ Katie Marsal (November 23, 2010). "Apple adds accelerometer, WebSockets support to Safari in iOS 4.2". AppleInsider.com. Archived from the original on 2011-03-01. Retrieved 2011-05-09.
- ^ "Web Sockets API". BlackBerry. Archived from the original on June 10, 2011. Retrieved 8 July 2011.
- ^ Chris Heilmann (December 8, 2010). "WebSocket disabled in Firefox 4". Hacks.Mozilla.org. Archived from the original on 2017-03-06. Retrieved 2011-05-09.
- ^ Aleksander Aas (December 10, 2010). "Regarding WebSocket". My Opera Blog. Archived from the original on 2010-12-15. Retrieved 2011-05-09.
- ^ Wang, Vanessa; Salim, Frank; Moskovits, Peter (February 2013). "APPENDIX A: WebSocket Frame Inspection with Google Chrome Developer Tools". The Definitive Guide to HTML5 WebSocket. Apress. ISBN 978-1-4302-4740-1. Archived from the original on 31 December 2015. Retrieved 7 April 2013.
- ^ "WebSockets (support in Firefox)". developer.mozilla.org. Mozilla Foundation. 2011-09-30. Archived from the original on 2012-05-26. Retrieved 2011-12-10.
- ^ "Bug 640003 - WebSockets - upgrade to ietf-06". Mozilla Foundation. 2011-03-08. Archived from the original on 2021-04-01. Retrieved 2011-12-10.
- ^ "WebSockets - MDN". developer.mozilla.org. Mozilla Foundation. 2011-09-30. Archived from the original on 2012-05-26. Retrieved 2011-12-10.
- ^ "Bug 640003 - WebSockets - upgrade to ietf-07(comment 91)". Mozilla Foundation. 2011-07-22. Archived from the original on 2021-04-01. Retrieved 2011-07-28.
- ^ "Chromium bug 64470". code.google.com. 2010-11-25. Archived from the original on 2015-12-31. Retrieved 2011-12-10.
- ^ "WebSockets in Windows Consumer Preview". IE Engineering Team. Microsoft. 2012-03-19. Archived from the original on 2015-09-06. Retrieved 2012-07-23.
- ^ "WebKit Changeset 97247: WebSocket: Update WebSocket protocol to hybi-17". trac.webkit.org. Archived from the original on 2012-01-05. Retrieved 2011-12-10.
- ^ "A hot Opera 12.50 summer-time snapshot". Opera Developer News. 2012-08-03. Archived from the original on 2012-08-05. Retrieved 2012-08-03.
- ^ "Welcome to nginx!". nginx.org. Archived from the original on 17 July 2012. Retrieved 3 February 2022.
- ^ "Using NGINX as a WebSocket Proxy". NGINX. May 17, 2014. Archived from the original on October 6, 2019. Retrieved November 3, 2019.
- ^ "Overview of new features in Apache HTTP Server 2.4". Apache. Archived from the original on 2020-11-11. Retrieved 2021-01-26.
- ^ "Changelog Apache 2.4". Apache Lounge. Archived from the original on 2021-01-22. Retrieved 2021-01-26.
- ^ "IIS 8.0 WebSocket Protocol Support". Microsoft Docs. 28 November 2012. Archived from the original on 2020-02-18. Retrieved 2020-02-18.
- ^ "Release-1 4 46 - Lighttpd - lighty labs". Archived from the original on 2021-01-16. Retrieved 2020-12-29.
- ^ "Release-1 4 65 - Lighttpd - lighty labs". Archived from the original on 2024-05-03. Retrieved 2024-05-03.
- ^ Christian Schneider (August 31, 2013). "Cross-Site WebSocket Hijacking (CSWSH)". Web Application Security Blog. Archived from the original on December 31, 2016. Retrieved December 30, 2015.
- ^ Peter Lubbers (March 16, 2010). "How HTML5 Web Sockets Interact With Proxy Servers". Infoq.com. C4Media Inc. Archived from the original on 2016-05-08. Retrieved 2011-12-10.
- ^ Willy Tarreau (2010-07-06). "WebSocket -76 is incompatible with HTTP reverse proxies". ietf.org (email). Internet Engineering Task Force. Archived from the original on 2016-09-17. Retrieved 2011-12-10.
- ^ Ian Fette (June 13, 2011). "Sec-WebSocket-Key". The WebSocket protocol, draft hybi-09. sec. 11.4. Retrieved June 15, 2011. Archived February 1, 2016, at the Wayback Machine
External links
[edit]- IETF Hypertext-Bidirectional (HyBi) working group
- RFC 6455 The WebSocket protocol – Proposed Standard published by the IETF HyBi Working Group
- The WebSocket protocol – Internet-Draft published by the IETF HyBi Working Group
- The WebSocket protocol – Original protocol proposal by Ian Hickson
- The WebSocket API Archived 2015-06-07 at the Wayback Machine – W3C Working Draft specification of the API
- The WebSocket API – W3C Candidate Recommendation specification of the API
- WebSocket.org Archived 2018-09-16 at the Wayback Machine WebSocket demos, loopback tests, general information and community